Integrated Technology Expertly Managed Personally Delivered
Everyone & Everything Connected since 1994
Our Incredible Partners


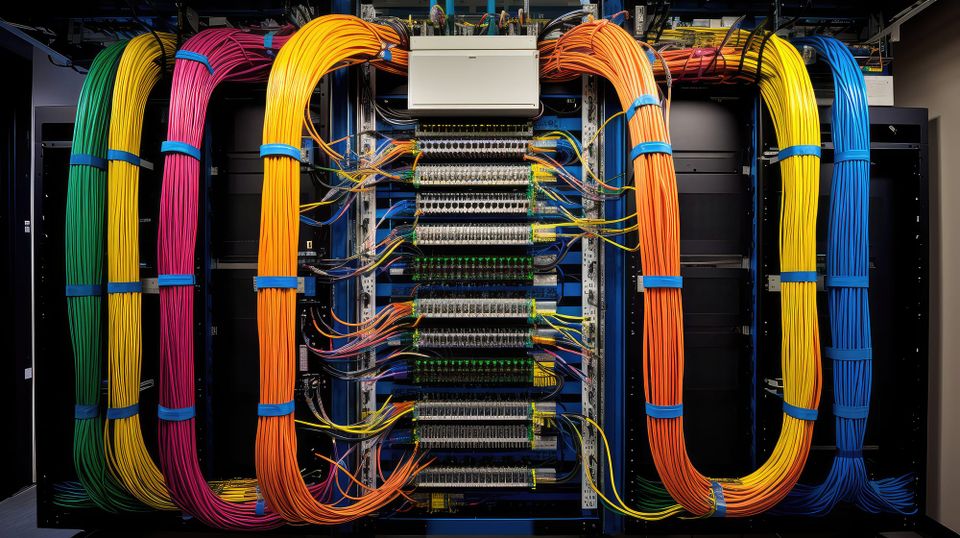
Since 1994, MORSECOM has helped organizations design, deploy, and support the technology systems they rely on every day. From infrastructure and networking to cybersecurity, communications, and physical security, we bring together the core elements of modern IT into a single, integrated approach. Our team supports businesses across Central Florida and the Space Coast while delivering solutions for organizations operating nationwide, ensuring consistent performance, security, and scalability at every level.
What sets MORSECOM apart is not just what we do, but how we do it. We take a hands-on, partnership-driven approach to every engagement, working closely with our clients to understand their operations, challenges, and long-term goals. Whether supporting a growing business, a multi-site enterprise, or a high-security environment, we deliver solutions that are thoughtfully designed, professionally implemented, and fully supported long after deployment.
Our customers are not just accounts. They are long-term partners. We believe in accountability, responsiveness, and doing things the right way the first time. From day-to-day support to complex project delivery, MORSECOM provides a level of service that feels personal, reliable, and consistent. When you work with us, you gain a team that is invested in your success and committed to keeping your organization connected, secure, and moving forward.